Identities (users)
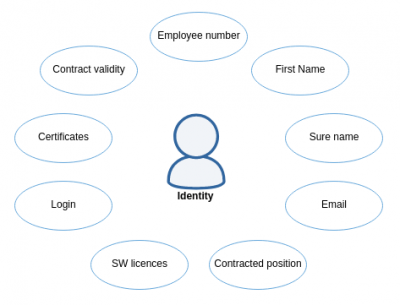
In identity management an identity is a set of informations that describes a real person. Some of the information like First Name, Last Name, Login or Password are crucial for many IT systems, since they process them, or e.g. use them for authentication or authorization. Identity management systems process the data about identity, transform them and use them to manage accounts on connected systems.
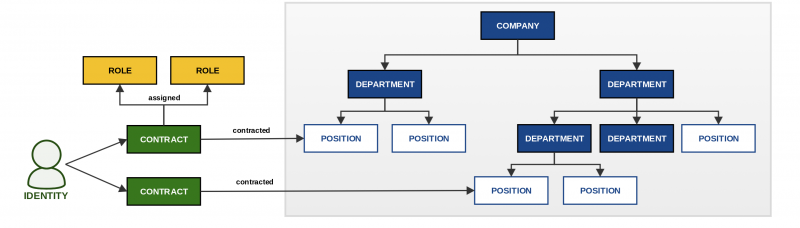
The representation of a user in CzechIdM system is an entity called identity. Put simply, an identity can be described as a user registered in CzechIdM with all his or her attributes e.g. first name, surname, phone number, etc. The identity representation is a rather complex discipline. To be able to handle automatic identity lifecycle processes, CzechIdM uses other entities with attributes that have a relation to an identity. Those are Contracts, Roles and Tree nodes forming Tree strucures.
Contracts
The relation of identities in CzechIdM to a company or organization is represented by an entity called contract. A contract can represent for example:
- job contract for work – employees
- study – pupils/students
- contract/arrangement – external co-workers
- etc.
A user can have multiple contracts. A contract is in relation with other objects in CzechIdM:
- Identity – described above
- Tree structure – a contract can be added to a tree (organizational) structure, which effectively allows integrating the user into a hierarchical division in an organization.
- Roles – roles in CzechIdM are assigned to contracts, i.e. a user gets roles through their contracts. Due to this, all manually created identities can have one automatically prepared contract called Default. (This can be disabled but is enabled by default.)
Identity state
Identity life cycle is controlled by identity's state. State is changed automatically by system - when an identity is created, a default contract to the identity is added.
Identity states:
- created - identity is enabled. State is assigned to a newly created identity.
- no contract - identity is disabled. Identity doesn't have a contract. All contract were deleted.
- future contract - identity is disabled. Identity has valid contract in the future, but not now.
- valid - identity is enabled. Identity has a valid contract.
- left - identity is disabled. Identity has invalid contracts only.
- excluded (~disabled) - identity is excluded (disabled). Identity contracts are excluded (assigned roles are not removed, when identity is excluded). This is usually used when the user has parental leave.
- disabled manually - identity is disabled manually, e.g. by administrator / synchronization. Manually disabled identity can be enabled again only manually (assigned roles are not removed, when identity is disabled manually).
When an identity becomes valid (i. e., at least one of their contracts becomes valid) and the identity has an account on at least one target system, then new password is generated and changed on all identity's accounts ⇒ identity will have the same password in all accounts. Notification (see acc:newPasswordAllSystems template) is sent to identity about which of their accounts were changed.
Password
In CzechIdM, user password is stored in Bcrypt hash function. User can change password only when he or she has permission IDENTITY_PASSWORDCHANGE for the given identity. Password contains also other metadata like valid till, valid from, unsuccessful attempts, block login date, last successful login etc. It is also possible to set flag Password never expires. This flag disables filling 'valid till'. 'Password never expires' and other attributes related to password like 'valid till' can be set via agenda information about password that is accessible through identity detail or password agenda. To update these attributes you will need permission PASSWORD_UPDATE and PASSWORD_READ.
Time slices of contracts
On many projects, we encounter a source of data about users, employees or org. structures that use so-called time slices. Slice is essentially a snapshot of a contract in a given period of time. To simplify working with time slices, an agenda of contract's time slices was created.
The basic idea is that time slices are stored in a self-contained agenda. This agenda only contains time slices for identity contracts. If a given slice is currently valid, its values will be copied into the linked identity contract. Every day, a scheduled task is performed, which calculates which slice is valid. Such a slice becomes currently used as a contract (its values are copied into the contract).
More information about contract time slices can be found in the developer guide here .
Protection of the validity of the contract
Sometimes there may be a situation where one of the time slices ends the contract, and at the same time there is a next time slice that restarts this contract. If there is no gap between termination and restart, then the contract will not be terminated (no accounts will be deleted). If the dates do not follow, then (by default) the contract will be terminated and all connected accounts will be removed from the target systems.
However, in some situations (projects), it is required to use the protection period for which the contract will not be terminated, provided that there is a next slice in the contract, which restarts the contract. Furthermore, it must be ensured that the gap between the termination and the beginning of the contract is shorter than or equal to the protection interval.
More information about this protection can be found in the developer guide here .